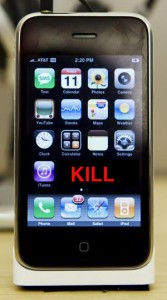
 Yahoo is reporting that Steve Jobs has admitted to the fact that Apple has installed a “kill switch” on the new iPhone that allows the company to take action to remotely remove an application from the device.
Yahoo is reporting that Steve Jobs has admitted to the fact that Apple has installed a “kill switch” on the new iPhone that allows the company to take action to remotely remove an application from the device.
According to the story Jonathan Zdziarski, author of the books iPhone Open Application Development and iPhone Forensics Manual, discovered a URL buried in Apple’s firmware that links to a file dubbed “unauthorized Apps” where malicious or simply bad apps might go once they disappear from the App Store.
Apple has already pulled several applications that were initially approved form the App Store including a tethering application called NetShare, a frivolous and stupid application called I Am Rich (if anyone bought this and you know them, please do us all a favor and take them out behind the chemical shed and shoot them for treason, sedition and really bad taste), and another application called BoxOffice.
It’s one thing to remove an application from the store but it seems to me to be altogether different to remove an application from someone’s device – particularly an application that someone paid for.
Jobs claims that the function is only there in case a malacious application is somehow distributed through the store but there have been many stores selling applications for years and never before has a kill switch been necessary to protect the consumer.
Of perhaps even greater concern is the fact that Apple didn’t admit this up front but only came clean when this was discovered by Zdziarski. One has to wonder if they ever would have revealed this sneaky inclusion in the firmware had the enterprising developer not done such a good job investigating the device.
Further it begs the question what else has Apple hidden in the iPhone 3G that we haven’t discovered yet? Are their invasive elements to the phone that make it easier to tap than another device? Is the device secretly logging history and reporting it back to Apple for contextual advertising? Is it logging my every step with the gps and figuring out where I go and when both to advertise more efficiently as well as for the more neferaious purposes of Homeland security.
The scary thing is that we can’t possibly be sure WHAT Apple has hidden in the code and we certainly can’t trust them to tell us the truth. They’ve already lied to us so many times that you think we’d be used to it by now and perhaps maybe we are. After all, no one bothered to delve into the bricking of the iPhones in much detail last year and Apple had another dirty secret that time around that I won’t even print for fear of reprisals.
Of course this also reaffirms Apple’s position as god – how many companies could get away with this and have a customer base left the following day. If someone found this kind of code in a Microsoft application or a Sony device (the rootkit debacle anyone?) we’d all be screaming bloody murder.
I love Apple gear as much as the next guy but isn’t it time we wiped the smug smile of their faces when they pull crap like this?
Remember when this was Apple’s image? [YouTube:http://www.youtube.com/watch?v=OYecfV3ubP8&autoplay=0 300 300]
Since when did they go from anti-establishment to being “big brother”?

I have to disagree with you. For hopefully obvious reasons. So long as they don’t abuse the killswitch, i’ll be happy that they have the ability to quickly kill an app that is known to be malicious.
i think you are hugely exaggerating this. It is disingenuous to bring in the Sony rootkit incident because Apple make the iPhone and the AppStore – its their product and they are responsible for ensuring it remains secure, both at the point of purchase of the app and after that fact. Whereas Sony installed the rootkit by simply inserting a CD into your computer.
John, Nokia has sold hundreds of millions of phones that can have software installed on them. They don’t feel the need to put a remote kill switch on their devices yet, in spite of not doing this there has not been one single report of anything like a malicious application run amok such that they needed to shut down the software on hundreds of thousands of devices simultaneously.
You are far too trusting if you think that the only reason that Apple wants this functionality is to prevent a malicious application. My guess is that they are just as likely to use it to shut down something like the NetShare Tethering application or even an application that allows you to install third party software that you didn’t get through the app store.
You said: “its their product and they are responsible for ensuring it remains secure”
No John, once you plunk down your hard earned cash and take that phone home it is no longer their product. It is a product they made but it is now YOUR PRODUCT. You exchanged cash for it and now you own it and owning something gives you certain inalienable rights. Rights that I believe are being violated by Apple’s undisclosed monitoring of the applications on your device and their hidden ability to disable them at will.
From my perspective, and I think that most people will agree, it’s your phone, shouldn’t it be your choice what software you have running on it? Just because Apple thinks a program should be shut down does not mean that I do.
I think you need to think about the potential repercussions of this a bit more before taking such a pro-Apple stance on this issue. If it was such an innocuous thing that Apple had done why didn’t they make it known to the public up front instead of only coming clean once it had been discovered hidden in the firmware?
Lastly, my reference to the Sony rootkit was not a direct comparison between what Apple did and what Sony had done – it was simply pointing out the damage that this incident did to Sony’s credibility whereas (and your comment is a case in point) Apple devotees are so blinded by love for this company that they are willing to accept almost any transgression or breach of trust and even choose to attack the messenger instead of the one responsible for the message.
Oliver
John, I just had another thought…
This move on Apple’s part may have just handed the keys to the Enterprise kingdom to Blackberry for good. I suspect that a lot of IT managers will now feel even more strongly that the iPhone isn’t a secure platform.
After all, if Apple has built in a back door such that they can snoop what products are running on a phone and even remove them remotely, what’s to stop someone from compromising this channel and taking data instead of turning off applications?
This is a really badly thought out move on Apple’s part and one for which I am now predicting they will pay dearly in the business marketplace.
Oliver
Oliver, the iPhone I have was received for free on an 18 month contract. Its not “mine” until I finish the contract.
Google “Symbian malware”. And Nokia has *not* sold hundreds of millions of phones with GPS built in together with a location based API (CoreLocation) free for developers to use. Its this level of privacy concern that more than justifies the need for a killswitch. What if a backend problem at say, Loopt became apparent that was broadcasting the exact locations of every iPhone Loopt user to the public? Do Apple wait for Loopt to fix the problem, exposing iPhone users co-ordinates to the world at large and suffering a disasterous PR storm? Or do they disable to app from working until Loopt fix it? I know as a user which I prefer.
If Apple revoke an app I have paid for that had no malicious intent, then I will rightly chastise them for it. They have to be *very* careful about how they use the killswitch as a PR storm could affect them. But until they actually use it for such a purpose who are you or I to judge them?
Its not an issue of being a devotee. The iPhone and Core Location gives consumers a new level of privacy concerns to think about. Apple as the guardian of the Appstore (the sole way to legitimately enable apps on your phone), takes sole responsibility for the inherent privacy you have on the phone. If Loopt or another SNS fuck up its Apple who vetted them for approval. a completely difference scenario to the Nokia/Symbian or Microsoft/Windows model.
John, I don’t know what plan you are on that you received your phone for free on an 18 month contract as that is not a plan that has been publicized to any degree where I am. However in the case of your device that phone still no longer belongs to Apple. Perhaps it could be argued that it belongs to the carrier but the truth is that if you cancel your service before you complete the contract term you still keep the phone. Perhaps you pay an early termination fee but at no time does the device revert to Apple.
As for “Symbian malware” sure there are lots of links in Google. There are hundreds of millions of Symbian devices out in the wild. Considering the number of Symbian devices the lack of malware has actually been pretty astonishing. Much as F-Secure and other companies would like us to believe that Symbian phones are as much at risk as windows PCs the reality is that there have been virtually no significant problems with malware on mobile devices to date.
Additionally there have been plenty of devices that have built in GPS enabling a third party to locate the phone or the user either with or without that user’s knowledge. Apple hasn’t written these applications and I am willing to bet that the language in the user agreement for the Apps Store and for iTunes absolves Apple of any responsibility for any problems that an end user might have with a third party application.
I don’t believe that people were successful in suing GM or Ford when their vehicles crashed as a result of faulty tires even though those tires had been installed by the manufacturer prior to the consumer taking delivery of the vehicle. No – the liability remained with the tire manufacturer much the same way that the liability for a flawed application would reside with the developer.
It is one thing for Apple to discover a flaw and issue a warning suggesting that the application be removed from the device but quite another for Apple to clandestinely put a mechanism in each device that allowed them to exert post-purchase control over what can or cannot remain on the device particularly considering the fact that what is on the device was likely put their using Apple’s pre determined mechanism for so doing, that Apple was paid for this application (if there was a fee for it) and, as I said initially that Apple no longer owns the device in question.
I also notice that you didn’t respond to my suggestion that this move on Apple’s part is likely the death of this device as a viable enterprise solution. IT managers are not going to tolerate manufacturer back doors into their environments especially back doors that at a minimum can disable or uninstall full applications and god only knows what else.
It is not difficult to imagine that a whole host of other data is being transmitted back to Apple in addition to that about which applications are on a particular device.
Finally, the fact that Apple didn’t disclose this right up front is another very significant indicator that Apple knew that this was not something legitimate nor something that people would appreciate.
If they thought it was then why didn’t they promote it as a safety feature baked right into their handset?
Why didn’t Steve Jobs say something like the following during his keynote at WWDC?
“Security is another issue that we take very seriously at Apple and we have created an additional, unique mechanism to insure that your device remains secure so that you can enjoy the knowledge that if Apple, at any time, learns that any application installed via the App Store is functioning in a way that could compromise the privacy, safety or security of the user or the data on the device, we have a built in mechanism that will allow us to deactivate that malfunctioning code in real time.”
He could have said something like that but he didn’t. Why? Because they didn’t think of it? Or because they knew that lots of people would say “but wait a minute? How would they know what is running on my device? And how could they remotely deactivate a particular application? You know, I’m not so sure I like the idea of Apple acting as big brother on my phone.”
Actually now that I think about it this is an even greater about face then I had realized. Remember Apple’s “1984” Campaign?
Hasn’t Apple become more like “the establishment” and we like the “huddled masses” mindlessly accepting whatever Apple tells us is cool?
Think about it. Do you really want Apple to know or monitor everything that is going on with your phone? If not, how do you know that they aren’t?
Oliver
This rant demonstrates an incoherent thought process from someone with too little technology savvy but blessed with an overactive imagination. A little knowledge can be a dangerous thing, as in this case. Clearly the writer demonstrates poor knowledge of how cellphone triangulation works, for example, because had even a glimmer penetrated the darkness of his ignorance he would realize the signal provider (Apple is the signal processor) knows precisely where you are at all times, no matter what phone you use. And the use of remote kill is simply an example of a facility demanded by corporate IT managers; namely the ability to remotely wipe a stolen iPhone. The reasons for this are obvious. So, far from precluding the iPhone from corporate uses, this facility actually makes it practicable.
@StefTheRef,
Actually, Stef, your comment demonstrates a lack of comprehension of my article rather than my inability to understand what is happening with the handset..
I never said anything in my article about the signal provider (who would typically be AT$T with a locked, US Phone) nor was I talking about wiping a device that has “gone missing’.
Both of these facets of mobile device operation and management are well known and generally accepted by end users and corporate IT managers. Instead what I was writing about, and what you failed to grasp correctly – was Apple’s “baked in” ability to selectively kill any application running on the device that they choose to kill.
This “killing’ of an application could take place regardless of whether the device was listed as missing or not, regardless of whether the device was locked or unlocked and regardless even of whether the application in question was purchased, downloaded for free, and even if it was downloaded via Apple’s “Official Channel’ the iPhone App Store.
Contrary to your contention that my “unfounded rant” fails to describe the general consensus view of corporate IT managers about this previously undisclosed capability that Apple left for itself – it is a specific reason cited by a number of such individuals as to why they do not allow the device to be part of their corporate networks..
You see, unlike wiping a missing device, which is an executable command that causes a device to erase all data and does not require any server side knowledge of what is on the device, Apple’s ability to kill a particular application requires that Apple knows that said application is resident on the phone. This means that by default the device is either reporting back to Apple via an undisclosed data conduit or that Apple has the ability to remotely probe devices to check for apps that they’ve decided to disallow. Neither of these circumstances is acceptable to security conscious IT administrators when it comes to their networks or the gear that accesses them.
In the future, if you’re going to accuse a writer of failing to comprehend his or her subject matter, do yourself the favor of at least reading the article in its entirety and being sure that YOU UNDERSTAND WHAT WAS WRITTEN, before you take exception to it and then prove by virtue of your critical comment that it is your thought processes that have failed to be coherent and that you haven’t the faintest idea what you are talking about..
Oliver Starr
PS: I hope you are not one of the aforementioned corporate IT managers because if you are and your capabilities are evidenced by your comment and misunderstanding of the danger inherent in Apple’s “kill switch” security flaw, your network, your job, or both are in grave danger.
It comes as no surprise to me that apple has gone behind the consumers back and implanted a code to take control of your device. Apple is a fuck. They always dick people around. My knowledge of this can be traced back to the first generation Ipod; Having the technology to build a better product, apple will build a shittier product than the current technology, advertise the fuck out of it with their people dancing and everyone smiling about how happy the “NEWEST AND GREATEST IPOD YET” makes them and how much better their life is because they have become part of the technological wave.
Always the same song and dance from apple. The message I get is “fuck you consumer. I am steve jobs,leader of the technological revolution. Deposit your dues at any one of our convenient locations.” To support my stance I will use the iphone (as it is the most recent and easiest for most people to grasp). When the iphone was designed (the origional “5 years ahead of the competition, omfg omfg its a touch screen iphone)AT&T was long done with the EDGE network and well into sales of 3G network ready phones,as the 3g network was in place and ready for the volume. Apple, however (dickin’around) first designing, then producing a phone with software already ready for the 3g infrastructure proves my point. There is nothing to prohibit apple from putting a $4 radio in their $600 phone from day one. Nothing except wanting to sell the same product to the same person 4 times in a period of about 2 years. (that would be Iphone, Iphone 32GB, Iphone 3g,Iphone 3gs{3gs makes some new developments, but still maintains most of the original equipment from iphone, only thing new is faster processor and more ram}) So in other words apple is dickin around. Its not about the customer. It was never about the customer to apple. Apple isn’t supplying the demand of a population, Steve is growing an empire on the backs of those with “more important things to do than worry about the limitations of their electronic devices.
…!!!! and why do they try sooooo hard to make sure that you cant put songs on and take songs off of your ipod where and when you please!!!
that is standard on almost every MP3 player to date. Nope, not for ol dickin around apple’s products. Bend over consumers… steve is here.
WHY CANT THE WORLD SEE THAT R.I.M. IS THE BEST THING TO EVER HAPPEN TO MOBILE TECHNOLOGY!!!
Granted, they need some new designs… the storm was a step in the right direction. albeit a baby step, but a step and with the **New Technological application of piezo-technology**
RIM is almost finished developing the ODIN device coupled with the latest Blackberry software the next step could be a giant leap. (fingers crossed)
one thing remains. Research In Motion is and has been the standard for mobile security.
The BlackBerry solution focuses on containing malicious programs. The BlackBerry software and all of the core applications are digitally signed to ensure integrity and control access to the Application Programming Interfaces (APIs). Thus, the core BlackBerry functionality cannot be directly accessed by other applications. (Blackberry.com)
I’m not in any way compensated for my findings, I have simply become aware that maintaining security is the responsibility of the individual. Since we the consumers don’t make the devices it is absolutely crucial that we maintain a knowledgeable understanding of Trust in a company. Apple does not satisfy my understanding of Trust. Nor have they ever.
All I have for the iphone is a BMG.50.
There’s some great tips there, just blogged about it too!